What is a Consensus Mechanism?
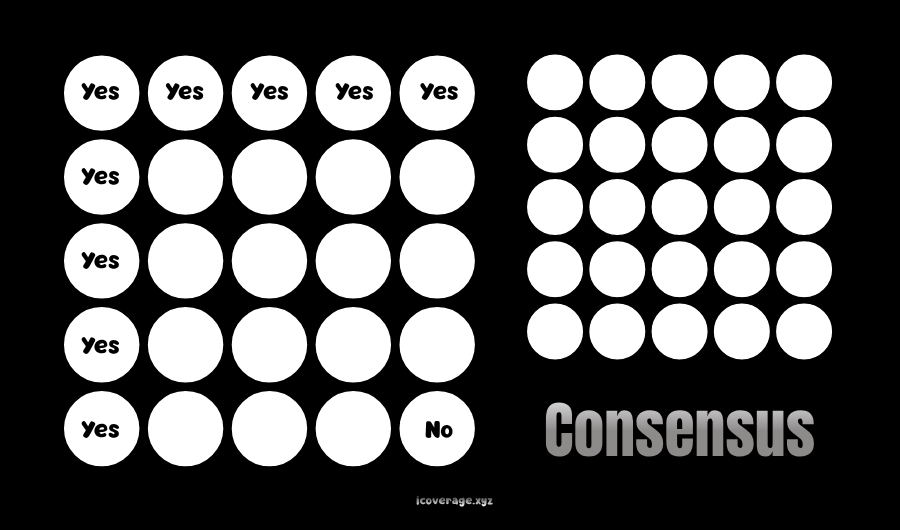
A consensus mechanism is the protocol that enables distributed systems to agree on a single, shared state without central authority.
Defining Consensus Mechanisms
In distributed computing, a consensus mechanism is a formal process through which independent nodes in a network agree on the validity of data and the order in which it is recorded. This agreement is essential in environments where no single party is trusted to maintain authoritative control. The concept originates from distributed systems theory, where achieving agreement among unreliable or geographically dispersed processes is a foundational challenge.
In blockchain systems, consensus mechanisms determine how transactions are validated, how new blocks are added, and how conflicts are resolved when multiple versions of a ledger temporarily exist. The mechanism ensures that every participant ultimately converges on the same version of the ledger, preserving consistency across the network. Without such a protocol, decentralized systems would fragment into incompatible states, rendering them unreliable.
The Problem of Distributed Agreement
The need for consensus mechanisms arises from the inherent difficulties of coordinating distributed systems. Nodes may fail, messages may be delayed, and some participants may act maliciously. The classical formulation of this challenge is captured in the Byzantine Generals Problem, introduced by Leslie Lamport, Robert Shostak, and Marshall Pease in 1982. The problem demonstrates how participants in a distributed system can reach agreement despite the presence of faulty or adversarial actors.
Consensus mechanisms address this problem by defining strict rules for communication, validation, and decision-making. These rules ensure that honest participants can reach agreement even when a subset of nodes behaves unpredictably. The system’s resilience is typically measured by its fault tolerance, which specifies the proportion of nodes that can fail or act maliciously without compromising the integrity of the network.
Core Properties of Consensus
A well-designed consensus mechanism satisfies several fundamental properties. Consistency ensures that all honest nodes agree on the same state of the system. Liveness guarantees that the system continues to process transactions and does not stall indefinitely. Fault tolerance defines the system’s ability to operate correctly despite node failures or adversarial behavior.
These properties are not merely theoretical constructs; they are formal requirements studied extensively in distributed computing. For example, Lamport’s Paxos algorithm and the Raft consensus algorithm, developed by Diego Ongaro and John Ousterhout, provide rigorous frameworks for achieving consensus in distributed systems. While these algorithms are not typically used in public blockchains, they establish the theoretical foundation upon which modern consensus mechanisms are built.
Consensus in Blockchain Systems
Blockchain networks apply consensus mechanisms to maintain a decentralized ledger. Each node independently verifies transactions and participates in the process of adding new blocks. The consensus protocol ensures that only valid transactions are included and that all nodes agree on their order.
In such systems, consensus must address two critical challenges simultaneously. It must prevent double-spending, where a single digital asset is spent more than once, and it must ensure that all nodes maintain a consistent transaction history. These requirements are particularly stringent because blockchain networks operate in open environments where participants may join or leave at any time.
Proof of Work
Proof of Work is one of the earliest and most widely recognized consensus mechanisms. It was popularized by the Bitcoin network, introduced by Satoshi Nakamoto in 2008. In this system, nodes known as miners compete to solve computationally intensive puzzles. The first node to solve the puzzle earns the right to add a new block to the blockchain and receives a reward.
The security of Proof of Work is derived from the computational effort required to produce blocks. Altering the blockchain would require an attacker to redo the work for all subsequent blocks, which becomes increasingly impractical as the chain grows. This mechanism effectively deters malicious activity by making attacks economically unfeasible.
However, Proof of Work has notable limitations. Its reliance on intensive computation leads to significant energy consumption. This has prompted criticism and motivated the development of alternative consensus mechanisms that aim to achieve similar security guarantees with lower resource requirements.
Proof of Stake
Proof of Stake replaces computational effort with economic stake as the basis for consensus. In this model, participants known as validators lock up a certain amount of cryptocurrency as collateral. The protocol selects validators to propose and validate new blocks based on their stake and other criteria.
Ethereum transitioned from Proof of Work to Proof of Stake in 2022 through an upgrade known as “The Merge,” implemented by the Ethereum Foundation. This transition significantly reduced the network’s energy consumption while maintaining its security model.
The security of Proof of Stake relies on economic incentives and penalties. Validators are rewarded for honest behavior and penalized, often through a process called slashing, for malicious actions. This creates a system in which participants are financially motivated to maintain the integrity of the network.
Delegated and Hybrid Mechanisms
Beyond Proof of Work and Proof of Stake, numerous variations and hybrid approaches have been developed to address specific performance and governance requirements. Delegated Proof of Stake, for example, allows token holders to vote for a limited set of delegates who are responsible for validating transactions and producing blocks. This model is used by platforms such as EOS, developed by Block.one.
Hybrid mechanisms combine elements of multiple consensus models to balance security, scalability, and decentralization. Some systems integrate Proof of Work with Proof of Stake, while others incorporate additional layers of validation or governance. These designs reflect ongoing experimentation in the field, as developers seek to optimize consensus for different use cases.
Practical Byzantine Fault Tolerance and Variants
Practical Byzantine Fault Tolerance, introduced by Miguel Castro and Barbara Liskov in 1999, is a consensus algorithm designed for systems with a known set of participants. It allows a network to reach agreement even if up to one-third of the nodes are faulty or malicious.
This approach is particularly well-suited to permissioned blockchain networks, where participants are authenticated and controlled. Systems such as Hyperledger Fabric, developed by the Linux Foundation, employ variants of Byzantine fault-tolerant consensus to achieve high throughput and low latency.
Unlike Proof of Work or Proof of Stake, which operate in open and permissionless environments, Byzantine fault-tolerant mechanisms rely on a more structured network model. This distinction highlights the importance of aligning the consensus mechanism with the intended use case of the system.
Trade-offs in Consensus Design
No consensus mechanism achieves all desirable properties simultaneously. Designers must navigate trade-offs between security, scalability, and decentralization. This tension is often referred to as the blockchain trilemma, a term popularized by Ethereum co-founder Vitalik Buterin.
Proof of Work offers strong security and decentralization but struggles with scalability and energy efficiency. Proof of Stake improves efficiency but introduces new considerations related to wealth concentration and governance. Byzantine fault-tolerant mechanisms provide high performance but are typically limited to smaller, permissioned networks.
These trade-offs are not merely theoretical; they influence the practical deployment and adoption of blockchain systems. Each mechanism represents a different balance of priorities, shaped by the specific goals and constraints of the network.
Security Considerations
The security of a consensus mechanism depends on its ability to withstand various forms of attack. In Proof of Work systems, a 51 percent attack occurs when a single entity controls the majority of the network’s computational power. In Proof of Stake systems, similar risks arise if a participant controls a majority of the staked assets.
Other attack vectors include network partitioning, where communication between nodes is disrupted, and long-range attacks, which exploit historical data to alter the blockchain’s state. Consensus mechanisms incorporate safeguards to mitigate these risks, but no system is entirely immune.
Formal verification and rigorous testing play a critical role in ensuring the reliability of consensus protocols. Academic research and real-world deployment continuously inform improvements in design and implementation.
Beyond Blockchain
While consensus mechanisms are most commonly associated with blockchain technology, their applications extend to other areas of distributed computing. Databases, distributed file systems, and cloud infrastructure rely on consensus algorithms to maintain consistency and reliability.
For example, Google’s Spanner database uses a combination of consensus protocols and synchronized clocks to achieve global consistency. Similarly, Apache Kafka employs consensus mechanisms to coordinate distributed data streams. These applications demonstrate that consensus is a fundamental concept with broad relevance beyond cryptocurrencies.
Conclusion
Consensus mechanisms are the foundation of trust in decentralized systems, enabling independent participants to agree on a shared reality without centralized control. Their design reflects decades of research in distributed computing, combined with ongoing innovation driven by the demands of modern blockchain networks. By defining how agreement is reached, validated, and maintained, consensus mechanisms ensure the integrity, security, and functionality of distributed systems across a wide range of applications.
Disclaimer: The content on this page and all pages of Icoverage.xyz are presented for informational purposes only and should not be considered finance or legal advice.
This page may contain affiliate promotions.
Informations published are not financial advice.
We use diverse first and third party softwares on our website.
If you found an error, misinformation, or something harmful or unusual on this page please report it now!
This page or pages of this website may contain affiliate links that earn us commissions when you use them at no additional cost to you.
© ICPF All Rights Reserved | sitemap




